Industrial Cybersecurity |
Is your plant floor vulnerable to cyberattacks? |
Assessing Risk to Networked Devices on the Plant Floor |
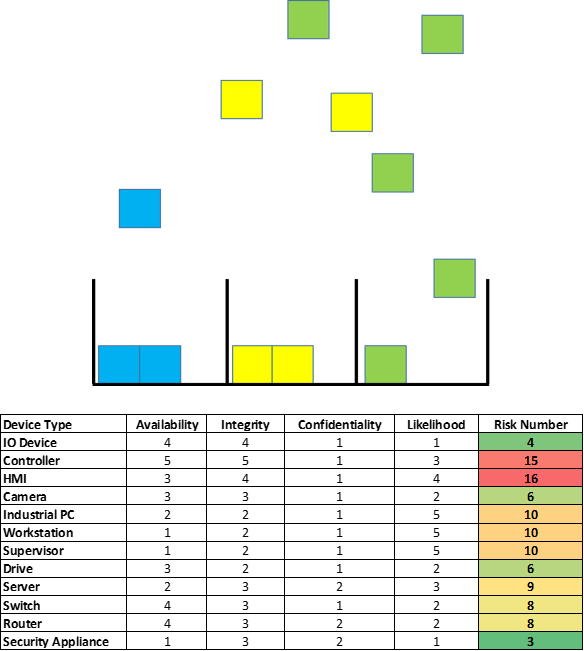
Hundreds to thousands of devices on the plant floor. Each type with their own level of cybersecurity risk. Device availability is critical to the production environment. What factors should be considered in an assessment? How to monitor and manage risks over the long term?
Upon completion of an asset inventory, the next step in establishing a cybersecurity program is to determine each device’s level of risk to a cyberattack. Many factors should be considered, including the type of device and on what level of the network it resides.
Identifying similarities across devices to improve efficiency is critical to a successful assessment and enabling the ongoing monitoring and patch management effort. Once this is completed, a prioritized action plan can be developed to secure plant floor devices. This information can also be used to create action plans when vulnerabilities are identified for groups of devices.
Key Considerations
- Divide assets into groups of similar type and function to simplify the process of evaluating each asset’s risk. Assets of the same type/ function carry the same level of risk.
- Utilize the AIC method, with the highest risk being Availability, followed by Integrity and Confidentiality, in contrast to standard IT risk analysis which uses the CIA (Confidentiality first) approach.
- The level on the network, as well as the overall network architecture, can have a significant impact on a given asset group’s risk level.
We can help!
Sandalwood has over 30 years’ experience working with global manufacturers helping them work smarter and work safer. Leveraging a standardized approach to achieve early sustainable value, we assist our clients to effectively apply their efforts to the right people, processes, and technology. Let us and our skilled partner network help you realize your vision.




 Why Sandalwood?
Why Sandalwood?


 We are a one-stop-shop for launching job rotation for any employer from conception to implementation. Our experts tailor our services to meet the needs of our customers by collaborating with them throughout the entire process. We do not offer cookie cutter solutions for job rotation because the needs of employers vary significantly.
We are a one-stop-shop for launching job rotation for any employer from conception to implementation. Our experts tailor our services to meet the needs of our customers by collaborating with them throughout the entire process. We do not offer cookie cutter solutions for job rotation because the needs of employers vary significantly. Why Sandalwood?
Why Sandalwood?


 Sandalwood is pleased to offer solutions above and beyond the traditional ergonomic assessments. With an in-depth knowledge of various digital human modelling software suites, integration and adoption to your health and safety programs has never been easier. Sandalwood is experienced in ergonomic program design as well as industry leaders in digital human modelling services. We have a diverse team that is able the leverage the results from the digital human model to provide in depth risk assessments of future designs and current state. Sandalwood is also able to pair these assessments with expertise and provide guidance on the best solution for you. Sandalwood is also on the forefront of emerging technologies and able to integrate Motion capture, Wearables, and extended or virtual reality into your ergonomic program.
Sandalwood is pleased to offer solutions above and beyond the traditional ergonomic assessments. With an in-depth knowledge of various digital human modelling software suites, integration and adoption to your health and safety programs has never been easier. Sandalwood is experienced in ergonomic program design as well as industry leaders in digital human modelling services. We have a diverse team that is able the leverage the results from the digital human model to provide in depth risk assessments of future designs and current state. Sandalwood is also able to pair these assessments with expertise and provide guidance on the best solution for you. Sandalwood is also on the forefront of emerging technologies and able to integrate Motion capture, Wearables, and extended or virtual reality into your ergonomic program.



